A modern authentication alternative to using service accounts in your Azure Active directory environment that may otherwise have to bypass basic authentication protections in order to perform unattended scripting operations.
Pros:
- Not needing to bypass the Modern Authentication enforcement in your Conditional access policies or MS365 settings.
Cons:
- Anyone with the certificate and application information could possibly authenticate to your exchange environment so the certificate should be highly guarded.
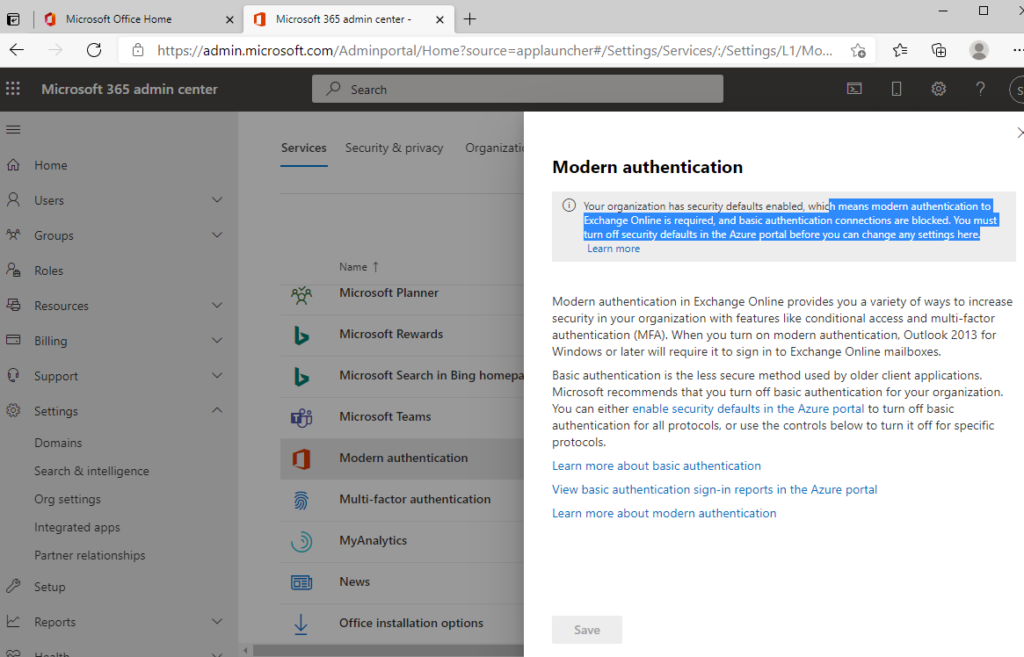
Checking if you have accounts on different Authentication profiles that are bypassing the security defaults. Powershell commands:
# Connect to Exchange
Import-Module -Name ExchangeOnlineManagement
Connect-ExchangeOnline
# Get all policies
Get-AuthenticationPolicy | Format-Table -Auto Name
# Get a particular users policy
get-user -Identity service_acct | select AuthenticationPolicy
# Set a particular users policy
Set-User -Identity service_acct -AuthenticationPolicy "Block Basic Auth"
DISCLAIMER: Please follow your own security protocols. This is just a demo.
Demo video on setting up an Azure Automation runbook to use a registered application.
This starts from building the automation account to finally executing a script that will connect to Exchange Online and perform commands.
- REF: https://docs.microsoft.com/en-us/powershell/exchange/app-only-auth-powershell-v2?view=exchange-ps#set-up-app-only-authentication
- REF: https://docs.microsoft.com/en-us/exchange/clients-and-mobile-in-exchange-online/disable-basic-authentication-in-exchange-online#create-and-apply-authentication-policies