How do we best detect the SpringShell vulnerabilty(CVE-2022-22965)?
Microsoft created a nice blog on the vulnerability here listing remediations and detection methods: https://www.microsoft.com/security/blog/2022/04/04/springshell-rce-vulnerability-guidance-for-protecting-against-and-detecting-cve-2022-22965/
Using this information and those of your Vulnerabiilty scanners we can start to discover legitimately vulnerable systems. There’s unfortunately a lot of false positives and so we might employ several tools which I’ll list here.
- To scan a suspect server for known suspect files there is this tool from qualys that scans Windows machines https://github.com/Qualys/spring4scanwin
- Nmap NSE script https://github.com/gpiechnik2/nmap-spring4shell
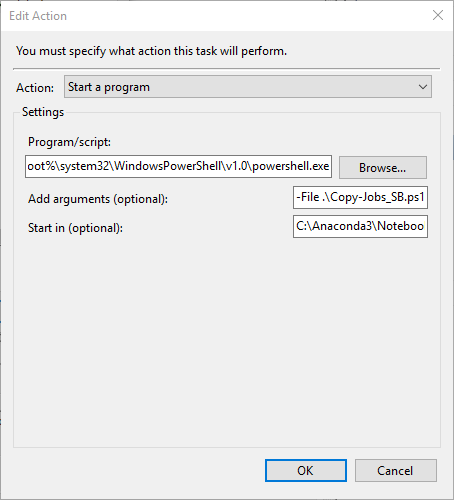
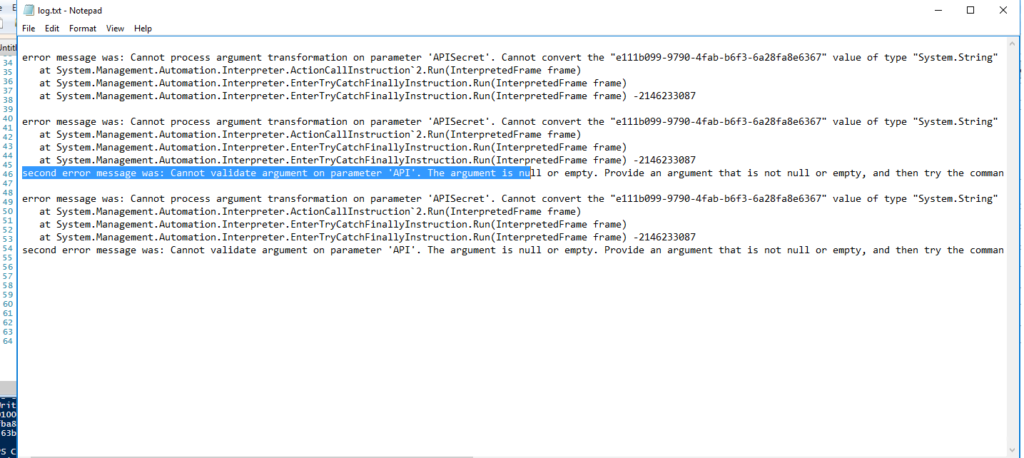
- Powershell script I created. It takes a csv file with an “Address” field that includes IP addresses to scan, using the known detection method as described in the MS report and others:
curl host:port/path?class.module.classLoader.URLs%5B0%5D=0
I use this scan external hosts for ports 80 and 443. You can modify this for your own use looking for a 400 http response. Also make sure to modify the export path so you can have a nice report of the hosts and their results.
Remediation/Mitigation
If you detect the vulnerable hosts you will need to apply patches for the spring framework or work with vendors to make sure apps are upgraded.
Spring Framework fixed releases:
- 5.3.18+
- 5.2.20+