This article is a part of my CCNA course material I use for study that encompasses everything needed to know about IPV6 as a layer 3 protocol to help pass the CCNA v3 exam. It is also a final consolidation of notes on the subject with full video and lab demonstration link provided to help the reader and myself better understand the subject. This will be updated as new information is disseminated.
Why IPV6
IPV6 is the next generation protocol that solves the IPV4 exhaustion problem that is currently being held together by CIDR and NAT as discussed in the article for IPV4. IPV6 like IPV4 has a many similarities but also many new features like new address types that allow for enhanced network communication. For example IPV6 clients can auto generate a Link Local Address to begin talking to each other on the network without admin intervention. With 128bits of address equaling 7038340000000000000♠3.4×1038 (340undecillion) addresses available to ipv6 this is like giving every atom on planet earth its own ip address 3x over. Now to sum up points for knowing everything needed on the CCNA see below.
Who made it
Registration with IANA > RIR(ARIN) > ISP > Your company ——must be made before using an ipv6 routable address/subnet. It will otherwise be dropped at some point in the routing process likely by the ISP or higher authority.
Characteristics
- 128 bits >32 hexadecimal digits > 8 sets of 4 hex digits(quartet) > 4 bits per digit >16 bits per set
ie; 11aa.22bb.33cc.44dd.55ee.66ff.7777.8888
Rules for ease of use:
- Abbreviate Leading 0s NOT trailing 0s i.e.; FE00:0000:0000:0001:0000:0000:0000:0056 = FE00:0:0:1:0:0:0:56
- Abbreviate consecutive quartets of 0s with double colons but only once ie; FE00:0:0:1::56
Review of Hex Numbering
Hex Binary Hex Binary
0 0000 8 1000
1 0001 9 1001
2 0010 A(10) 1010
3 0011 B (11)1011
4 0100 C (12)1100
5 0101 D (13)1101
6 0110 E (14)1110
7 0111 F (15)1111
IPV6 Header:
4 Bytes:
- version
- class
- flow label
- payload length
- next header
- hop limit
32 bytes
- source address – 16 bytes
- destination address – 16 bytes
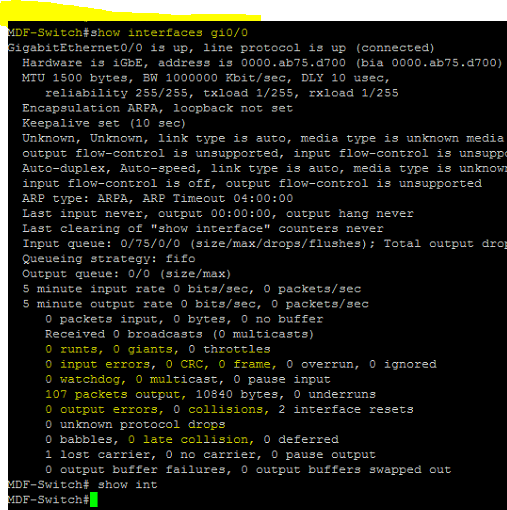
How it Works on Cisco Routers
When enabled on the router and on an interface (see below for commands):
- enables routing of IPV6 packets
- defines ipv6 prefix that will be used on that interface;
- adds a connected route to the routing table when the interface is up/up
-Interfaces can have ipv6 link local and global addresses configured and in use on their interfaces with a special ipv6 enable command in the interface subcommand mode. They don’t need ipv6 enabled on the router necessarily
Dual Stack: Terminology used when routers run both ipv4 and ipv6 routing and use a separate Routing table for each
Address Types
Global Routing Prefix:
Closest thing similar to IPv4s classful networks but in this case the company is locked down to using the network mask assigned by the IPV6 authorities so there really is no classes the address block that can be assigned to a company for which can also be addressed to when reaching that company. The prefix should allow the company to basically assign as many addresses as needed and so provides for that many
ie; Host: 2001:0DB8:1111:0001:0000:0000:0000:0001/64——-this allows for 2^64 =18446744073709551616 hosts
prefix length: 2001:0DB8:1111/48-first 12 hex digits
Prefix ID: 2001:DB8:1111:1::/64-keep in mind that 16 bits are used to represent the subnet id allowing for 2^16=65536 subnets
next prefix id: 2001:DB8:1111:2::—–this will go on until the 4 hex digits all reach the max allowed 16 bits using the hex digit 15
final prefix id: 2001:DB8:1111:FFFF–
Prefix ID:(same as subnet ID)
ie; /64 is the first 16 hex characters of the 128 bit/32hex address
ie; 2000:1234:5678:9ABC::/64 is the Prefix ID of 2000:1234:5678:9ABC:1234:5678:9ABC:1111/64
Global Unicast Address:
- Originally began with 2 or 3.
- Any unicast addresses not specifically reserved are considered global unicast.
- registered addresses with IANA that allow an organization to assign all their hosts public addresses
- EUI 64: Extended unique identifier: is a method to generate a unique interface ID after custom making the prefix
- -Inserts FFFE hex digits directly between the 12 hex MAC address of the interface to help make a unique 64 bit/16 hex address
- -Finally the 7th bit in the new interface ID(in second hex digit) is inverted(if its 1 make 0 if its 0 make 1). Reading left to right keep in mind
- -For serial interfaces without MAC addresses the router will use the MAC of the lowest numbered interface with a MAC
Unique Local Unicast Address:
- Begin with FD 8bits > next 48 bits(10 hex) needs to be the global prefix(can randomly make this) > next 16 bits is the subnet field to be used >finally 64 bits for the hosts
- RFC4193 requests that use of 8th bit should be 1 and so originally FC00::/7 is what IANA reserve
- Assign a Global ID and Prefix ID(in this case everything is in control of the engineer except for the first 8bits which need to be FD)
- Not registered and can be used any agency
- like ipv4 private addresses don’t need registration
Link Local:
- Begin with FE8;FE9;FEA;or;FEB
- -First 10 bits need to match FE80::/10
- -Next 54 bits need to be Binary 0s ie; FE80:0000:0000:0000/64
- -Next 64 bits can use EUI-64 method to autogenerate; OR can be manually entered OR can use Microsofts Algorithym
- Used for overhead protocols and for routing ie;NDP uses this type of address
- Unicast address
- Not forwarded by routers therefore only stays in the subnet locally
- Also used as a next hop address by routers in the same subnet and as the default gateway for hosts
- Automatically generated using EUI-64 when an interface is configured with any other ipv6 unicast address
Site Local Addresses:
- No longer a part of the IPV6 standard begin with FEC;FED;FEE or FEF
Multicast Adddresses:
Configured when a corresponding protocol is enabled
Begin with:
- FF02::1—-used to addres all ipv6 interfaces on the subnet
- FF02::2—-used to address all ipv6 router interfaces on the subnet
- FF02::5—-used to address all OSPFv3 Routers on the subnet
- FF02::6—-used to address all OSPFv3 DR routers on the subnet
- FF02::9—-used to address all RIPng Routers on the subnet
- FF02::A—-used to address all EIGRPv6 routers on the subnet
- FF02::1:2–used to address all DHCPv6 Relay agent Routers on the subnet
Solicited-Node Multicast Addresses
Anycast Addresses
- Begin With: These addresses can be any unicast address; Must use a host mask of /128 and are specified as anycast aaddresses in the ios
- Provide a service that may be spread among different routers/devices but is used to contact the nearest device when the service is called upon by a host
Subnet Router Any Cast Addresses:
- Used by routers to send packets to any other router on the subnet
- contains same prefix and all binary 0s for the interface ID
Unknown/unspecified Address:
- :: or all 0s
- Used as the source ip address when a host doesn’t know its address ie; in the case of using dhcp
Loopback address:
- ::1 or 127
- used to test the ipv6 stack
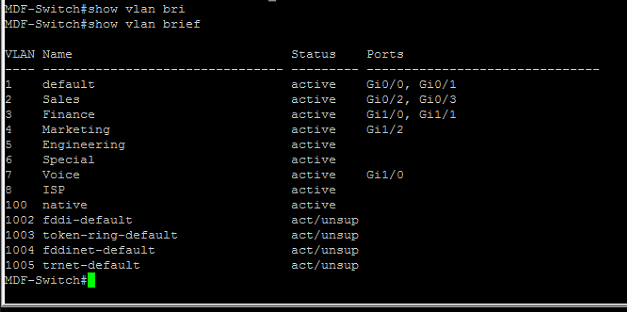
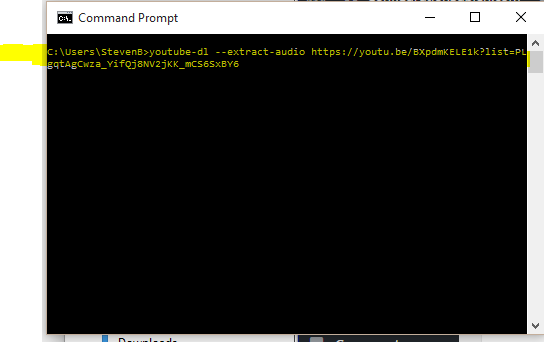
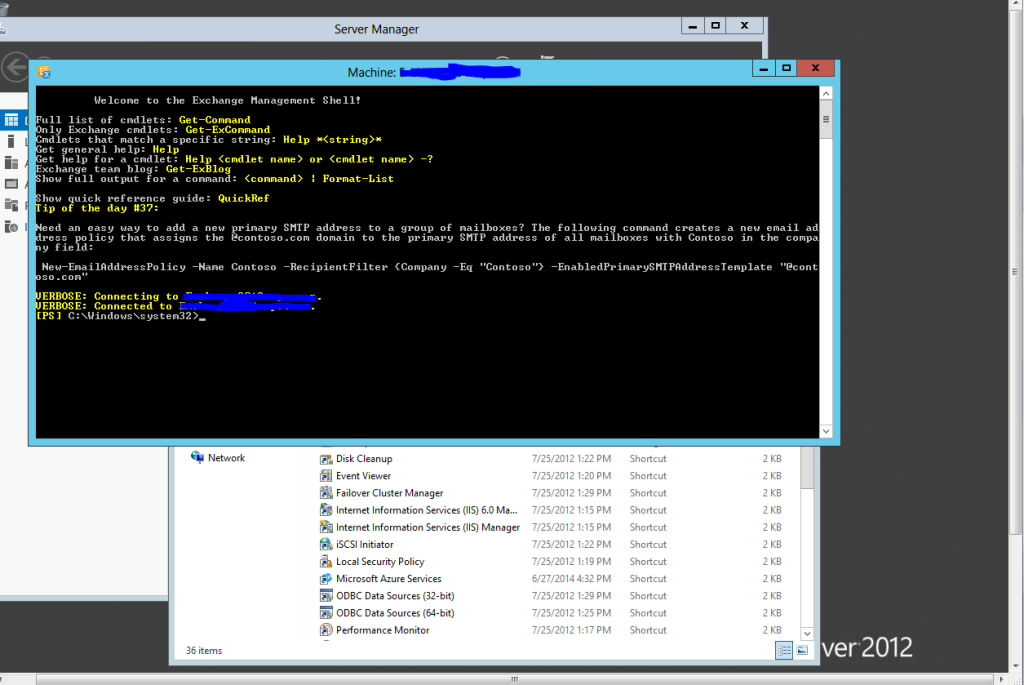
IOS Commands
Video(coming soon)